4. Understanding Advanced Exchange Server Permissions
Active Directory objects are assigned a set of permissions. These permissions are standard Microsoft Windows permissions, object-specific permissions, and extended permissions.
Table 3
summarizes the most common object permissions. Keep in mind that some
permissions are generalized. For example, with Read Value(s) and Write
Value(s), Value(s) is a placeholder for the actual type of value or
values.
Table 3. Common Permissions for Active Directory Objects
| PERMISSION | DESCRIPTION |
|---|
| Full Control | Permits reading, writing, modifying, and deleting |
| List Contents | Permits viewing object contents |
| Read All Properties | Permits reading all properties of an object |
| Write All Properties | Permits writing to all properties of an object |
| Read Value(s) | Permits reading the specified value(s) of an object, such as general information or group membership |
| Write Value(s) | Permits writing the specified value(s) of an object, such as general information or group membership |
| Read Permissions | Permits reading object permissions |
| Modify Permissions | Permits modifying object permissions |
| Delete | Permits deleting an object |
| Delete Subtree | Permits deleting the object and its child objects |
| Modify Owner | Permits changing the ownership of the object |
| All Validated Writes | Permits all types of validated writes |
| All Extended Writes | Permits all extended writes |
| Create All Child Objects | Permits creating all child objects |
| Delete All Child Objects | Permits deleting all child objects |
| Add/Remove Self As Member | Permits adding and removing the object as a member |
| Send To | Permits sending to the object |
| Send As | Permits sending as the object |
| Change Password | Permits changing the password for the object |
| Receive As | Permits receiving as the object |
Table 4
summarizes Exchange-specific permissions for objects. If you want to
learn more about other types of permissions, I recommend that you read Windows Server 2008 Administrator's Pocket Consultant, Second Edition (Microsoft Press, 2010) or Windows 7 Administrator's Pocket Consultant (Microsoft Press, 2009).
Table 4. Extended Permissions for Exchange Server
| PERMISSION | DESCRIPTION |
|---|
| Read Exchange Information | Permits reading general Exchange properties of the object |
| Write Exchange Information | Permits writing general Exchange properties of the object |
| Read Exchange Personal Information | Permits reading personal identification and contact information for an object |
| Write Exchange Personal Information | Permits writing personal identification and contact information for an object |
| Read Phone and Mail Options | Permits reading phone and mail options of an object |
| Write Phone and Mail Options | Permits writing phone and mail options of an object |
Although you can use standard Windows permissions,
object-specific permissions, and extended permissions to control
Exchange management and use, Microsoft recommends that you use the new
role-based access controls instead. My recommendation is to use the
role-based access controls whenever possible in place of specific
permissions. However, you might want to duplicate the old style
permissions during your transition from Exchange 2003 or Exchange 2007
to Exchange 2010. This can simplify the transition by allowing you to
configure new Exchange groups, such as Organization Management or
Recipient Management, exactly as they are configured in the Exchange
2003 or Exchange 2007 organization. In this case, after you've ensured
permissions are configured as required for proper operations and support
of any applications that work with Exchange data, you can start
implementing a role-based model for your organization.
5. Assigning Advanced Exchange Server Permissions
In Active Directory, different
types of objects can have different sets of permissions. Different
objects can also have general permissions that are specific to the
container in which they're defined. For troubleshooting or fine-tuning
your environment, you might occasionally need to modify advanced
permissions. You can set advanced permissions for Active Directory
objects by following these steps:
Open
Active Directory Users And Computers. If advanced features aren't
currently being displayed, select Advanced Features on the View menu.
Right-click the user, group, service account, or computer account with which you want to work.
Warning:
Only administrators with a solid understanding of Active Directory and Active Directory permissions should manipulate advanced object permissions.
Incorrectly setting advanced object permissions can cause problems that
are difficult to track down and may also cause irreparable harm to the
Exchange organization.
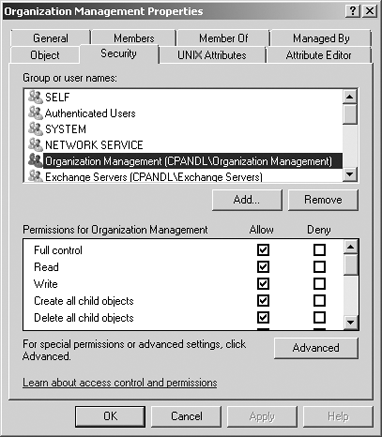
Select Properties from the shortcut menu, and then click the Security tab in the Properties dialog box, as shown in Figure 4.
Users
or groups with access permissions are listed in the Group Or User Names
list box. You can change permissions for these users and groups by
doing the following:
Select the user or group you want to change.
Use the Permissions list box to grant or deny access permissions.
When inherited permissions are dimmed, override inherited permissions by selecting the opposite permissions.
To
set access permissions for additional users, computers, or groups,
click Add. Then use the Select Users, Computers, Security Accounts, Or
Groups dialog box to add users, computers, security accounts, or groups.
Select
the user, computer, service account, or group you want to configure in
the Group Or User Names list box, click Add, and then click OK. Then use
the fields in the Permissions area to allow or deny permissions. Repeat
this step for other users, computers, service accounts, or groups.
Click OK when you're finished.