Getting to Know the Registry’s Root Keys
The root keys are your
Registry starting points, so you need to become familiar with what kinds
of data each key holds. The next few sections summarize the contents of
each key.
HKEY_CLASSES_ROOT
HKEY_CLASSES_ROOT—usually abbreviated as HKCR—contains
data related to file extensions and their associated programs, the
objects that exist in the Windows Vista system, as well as applications
and their Automation information. There are also keys related to
shortcuts and other interface features.
The top part of this key contains subkeys for various file extensions. You see .bmp for BMP (Paint) files, .doc for DOC (Word or WordPad) files, and so on. In each of these subkeys, the Default
setting tells you the name of the registered file type associated with
the extension. For example, the .txt extension is associated with the txtfile file type.
These registered file types appear as subkeys later in the HKEY_CLASSES_ROOT
branch, and the Registry keeps track of various settings for each
registered file type. In particular, the shell subkey tells you the
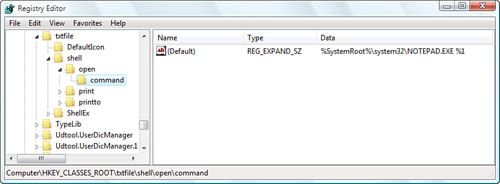
actions associated with this file type. For example, in the shell\open\command subkey, the Default setting shows the path for the executable file that opens. Figure 2 shows this subkey for the txtfile file type.
HKEY_CLASSES_ROOT is actually a copy (or an alias, as these copied keys are called) of the following HKEY_LOCAL_MACHINE key:
HKEY_LOCAL_MACHINE\Software\Classes
The Registry creates an alias for HKEY_CLASSES_ROOT to make these keys easier for applications to access and to improve compatibility with legacy programs.
HKEY_CURRENT_USER
HKEY_CURRENT_USER—usually abbreviated as HKCU—contains
data that applies to the user that’s currently logged on. It contains
user-specific settings for Control Panel options, network connections,
applications, and more. Note that if a user has group policies set on
his account, his settings are stored in the HKEY_USERS\sid subkey (where sid is the user’s security ID). When that user logs on, these settings are copied to HKEY_CURRENT_USER. For all other users, HKEY_CURRENT_USER is built from the user’s profile file, ntuser.dat.
Tip
How do you find out each user’s SID? First, open the following Registry key:
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\
Here you’ll find a list of SIDs. The ones that begin S-1-5-21 are the user SIDs. Highlight one of these SIDs and then examine the ProfileImagePath setting, which will be of the form %SystemDrive%\Users\user, where user is the username associated with the SID.
Here’s a summary of the most important HKEY_CURRENT_USER subkeys:
| AppEvents | Contains sound files that play when particular system events occur (such as maximizing of a window) |
| Control Panel | Contains settings related to certain Control Panel icons |
| Identities | Contains settings related to Outlook Express, including mail and news options and message rules |
| Keyboard Layout | Contains the keyboard layout as selected via Control Panel’s Keyboard icon |
| Network | Contains settings related to mapped network drives |
| Software | Contains user-specific settings related to installed applications and Windows |
HKEY_LOCAL_MACHINE
HKEY_LOCAL_MACHINE (HKLM)
contains non-user-specific configuration data for your system’s
hardware and applications. You’ll use the following three subkeys most
often:
| Hardware | Contains subkeys related to serial ports and modems, as well as the floating-point processor. |
| Software | Contains computer-specific settings related to installed applications. The Classes subkey is aliased by HKEY_CLASSES_ROOT. The Microsoft subkey contains settings related to Windows (as well as any other Microsoft products you have installed on your computer). |
| System | Contains subkeys and settings related to Windows startup. |
HKEY_USERS
HKEY_USERS (HKU) contains settings that are similar to those in HKEY_CURRENT_USER. HKEY_USERS is used to store the settings for users with group policies defined, as well as the default settings (in the .DEFAULT subkey) which get mapped to a new user’s profile.
HKEY_CURRENT_CONFIG
HKEY_CURRENT_CONFIG (HKCC) contains settings for the current hardware profile. If your machine uses only one hardware profile, HKEY_CURRENT_CONFIG is an alias for HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001. If your machine uses multiple hardware profiles, HKEY_CURRENT_CONFIG is an alias for HKEY_LOCAL_MACHINE\SYSTEM\ControlSetnnn, where nnn is the numeric identifier of the current hardware profile. This identifier is given by the Current setting in the following key:
HKLM\SYSTEM\CurrentControlSet\Control\IDConfigDB
Understanding Registry Settings
If
the left side of the Registry Editor window is analogous to Explorer’s
Folders pane, the right side is analogous to Explorer’s Contents pane.
In this case, the right side of the Registry Editor window displays the
settings contained in each key (so I’ll call it the Settings pane). The Settings pane is divided into three columns:
Name— This column tells you the name of each setting in the currently selected key (analogous to a filename in Explorer).
Type— This column tells you the data type of the setting. There are six possible data types:
REG_SZ— This is a string value.
REG_MULTI_SZ— This is a series of strings.
REG_EXPAND_SZ—
This is a string value that contains an environment variable name that
gets “expanded” into the value of that variable. For example, the %SystemRoot% environment variable holds the folder in which Windows Vista was installed. So, if you see a Registry setting with the value %SystemRoot%\System32\, and Windows Vista is installed in C:\Windows, the settings expanded value is C:\Windows\System32\.
REG_DWORD—
This is a double word value: a 32-bit hexadecimal value arranged as
eight digits. For example, 11 hex is 17 decimal, so this number would be
represented in DWORD form as 0x00000011 (17). (Why “double word”? A 32-bit value represents four bytes of data, and because a word in programming circles is defined as two bytes, a four-byte value is a double word.)
REG_QWORD—
This is a quadruple word value: a 64-bit hexadecimal value arranged as
16 digits. Note that leading zeros are suppressed for the high 8 digits.
Therefore, 11 hex appears as 0x00000011 (17) and 100000000 hex appears
as 0x1000000000 (4294967296).
REG_BINARY— This value is a series of hexadecimal digits.
Data— This column displays the value of each setting.