The next decision you have to make when putting
together the specifications for your network is the topology you want to use. The network topology describes
how the various nodes that the network comprises—which include not only
the computers, but also devices such as hubs and bridges—are connected.
Three common topologies are used in LANs: star, bus, and ring.
The Star Topology
The star topology, as you can see in Figure 1, consists of multiple workstations connected to a hub or
router. In the most common scenario, each computer has a network adapter
with an RJ-45 connector running a twisted-pair cable to a port in the
hub. The hub (usually) just passes along the signals, so each computer
gains access to the other computers on the network.
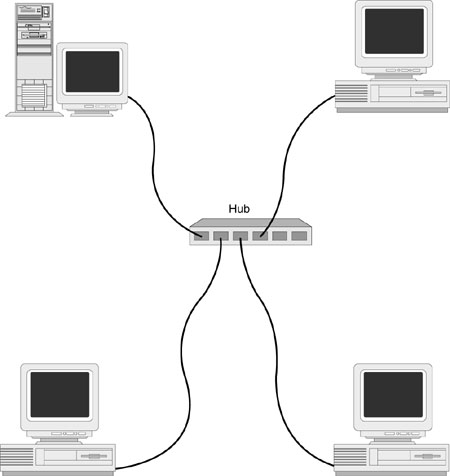
This is an excellent
topology for peer-to-peer networks because it mirrors the
no-machine-is-more-equal-than-any-other-machine philosophy of
peer-to-peer. It’s also easy to add machines to the network because it’s
a simple matter of running a new cable to the hub. If the hub’s ports
are used up, you can connect a second hub to the first one. Another
advantage of the star topology is that if one machine goes down for the
count, the network access of the other machines isn’t affected. On the
downside, star topology networks tend to need a lot of cable because you
have to connect every node directly to the hub.
The Bus
Topology
In a bus topology, shown in Figure 2, each node is attached to a single main cable called a bus or a
backbone. For large networks, the backbone often extends throughout an
entire building and is hidden behind the walls. For such lengthy cables,
repeaters are often needed to boost the signal along various points of
the backbone. Connections to the backbone are made via drop cables that
run from network cards to wall jacks or some other junction box.
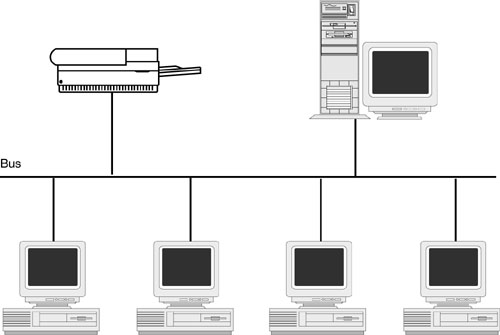
The big advantage of the
bus topology is that it’s relatively easy to set up (aside from the
effort required to run cable through a building’s walls), and its layout
often mirrors the physical layout of an office or a building. The major
drawback of the bus topology is that a break in the backbone brings
down the entire network.
The Ring Topology
At first glance, the ring
topology sounds suspiciously like the
star topology. Each network node is connected to a central device, which
is a special kind of hub called a multistation
access unit (MAU), as shown
in Figure 3. The difference lies in how the hub views the
network. In the star topology, when the hub receives a packet, it checks
the destination and then forwards the packet to the appropriate node
without worrying about any other node on the network. In the ring
topology, however, the circuitry of the MAU organizes the entire network
as a ring, and each received packet is broadcast around the ring.
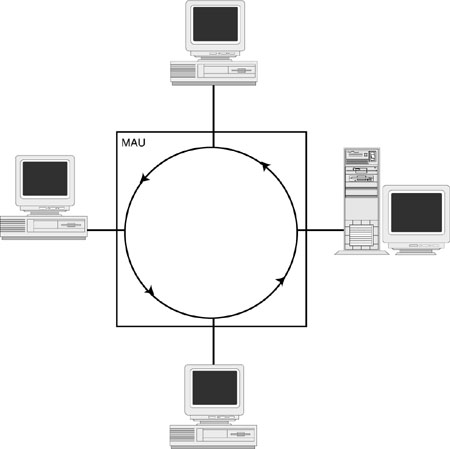
This is the topology used
in token ring and ARCnet networks. This makes sense because these
network architectures use a token-passing method to allocate cable
access. The ring structure is a very efficient way to pass the token
around to each node, so overall performance is improved.
Like star topologies,
ring topologies are more stable than bus designs because one node going
down doesn’t affect the entire network. There is one exception, however.
The ring topology requires that each node actively pass along each
packet. If a node goes down before it has had a chance to pass along a
packet, the entire network crashes. Such a situation, however, is
relatively rare.
Talking the Talk: Networking
Protocols
In diplomacy, protocol
defines the rules and formalities that ensure smooth communications
between nations and cultures. A networking
protocol performs a similar function: It’s a
set of standards that define how information is exchanged between two
systems across a network connection.
For example, consider
what appears to be a simple procedure: exchanging a file between two
networked computers. I mentioned earlier that files and all other
network transmissions are broken down into packets. Because a large file
might consist of hundreds or even thousands of packets, there has to be
some way of coordinating how all this information is sent and received.
Here are just a few of the questions that must be answered for even the
simplest file transfer to succeed:
| • | Which computer is sending the packets? |
| • | Where are the packets supposed to go? |
| • | What is the structure of each
packet? How big is the header? How big is each data field inside the
header? What order are the data fields in? What kinds of addresses are being used?
What kind of error checking mechanism is being used? Where does the data
start? |
| • | How many packets are in the transfer? |
| • | In what order should the packets be reassembled? |
| • | What happens if a
packet arrives damaged? |
| • | How long should the destination
computer wait for a packet to arrive? |
| • | What happens if a packet
hasn’t arrived after the allotted time? |
| • | How does the source
computer know that the destination computer has received a particular
packet and, eventually, the entire file? |
As you can see, it takes
an incredible amount of give-and-take to coordinate any kind of network
interaction. The inherent complexity of this process means that if the
source and destination systems are even slightly out of sync, the file
either will arrive corrupted or won’t arrive at all. Network protocols
are designed to ensure that this doesn’t happen. The protocol specifies
in no uncertain terms all the details of any kind of network transfer.
Generally speaking, protocols fall into two categories: transport
protocols and network protocols.
With a transport
protocol (also called a connection-oriented
protocol), a virtual communications
channel is established between two nodes, and the protocol uses this
channel to send packets between the nodes. Because the source and
destination are defined in advance, the packets need not contain full
address information. The constant link between the two nodes provides
the protocol with an efficient path for exchanging messages, so this
type of communications method is useful for applications that require a
long-term connection (such as a network monitoring program). However,
some overhead is involved in both setting up and closing the channel, so
this method isn’t suitable for short-lived communications.
With a network
protocol (also called a connectionless
protocol), no communications channel
is established between nodes. Instead, the protocol builds each packet
with all the information required for the network to deliver each packet
and for the destination node to reassemble the packets into the
original file. These self-contained independent packets are called datagrams. The protocol then ships out the packets without
notifying or negotiating with the destination node. All the network has
to do is transmit the packets to the destination or to some intermediate
stop along the way. This method requires a bit more packet overhead,
but it’s efficient for short bursts because there’s no need to set up or
shut down a channel between nodes.
Many protocols are available, but two are most
common (these are the standard protocols available with Windows XP):
| TCP/IP | TCP/IP stands for Transmission Control Protocol/Internet Protocol; TCP is the transport protocol, and IP is the
network protocol. TCP/IP is the lingua franca
of most UNIX systems and the Internet as a whole. However, TCP/IP is
also an excellent choice for other types of networks because it’s
routable, robust, and reliable. |
| IPX/SPX | IPX/SPX stands for Internet Packet eXchange/Sequenced Packet
eXchange. IPX is a
connectionless network layer protocol. As a network layer protocol, IPX
addresses and routes packets from one network to another on an IPX
internetwork. SPX, on the other hand, is an extension of IPX that
provides for connection-oriented transport layer functions. SPX enhances
the IPX protocol by providing reliable delivery. IPX/SPX is used by
NetWare networks. |
When setting up your
network, you don’t have to commit to a single protocol. Windows XP is
happy to work with multiple protocols simultaneously, so you don’t have
to box yourself in. This is particularly handy in network environments
that must access different types of machines. You can use IPX/SPX to
access a NetWare server, and TCP/IP to access UNIX boxes, most Windows
clients, and the Internet. However, most small networks operate best by
using only TCP/IP.