Backing Up Active Directory
Active Directory domain
controllers contain a copy of the database that stores all Active
Directory-related information. This is stored by default on the C: drive
but it is included in the System State and Bare Metal Recovery backup.
Also critical on Active Directory servers are the files and folders
stored in the sysvol folder on the boot drive. The sysvol folder is also
included in a System State backup. To properly back up a domain
controller, a full backup should be scheduled to run nightly or multiple
times per day. In addition to scheduled backups, text file exports and
securing the most important objects can assist with reliability as well
as recovery efforts. If full backups cannot be performed daily due to
time or backup storage constraints, taking daily System State backups
would be sufficient for Active Directory recovery, but might not provide
enough protection to recover the entire domain controller after a
hardware issue or serious software problem.
LDIFDE and CSVDE Command-Line Tools
Ldifde.exe and csvde.exe
are two command-line utilities that can be used to export and import
Active Directory object information. For example, these tools can be
used to export a list of all user accounts, groups, organizational units
(OUs), and computer objects in an Active Directory domain.
When a restore of a deleted object
is required, or when an object’s attribute or property values are
changed, having a text file export to reference the original location
and distinguished name of the object, or the values of the object’s
attributes, is very valuable. To restore a single object, or an OU with
all the objects contained within the OU, the distinguished name (DN) of
the object is required. Using LDIFDE or CSVDE to export objects to a
text file will contain the DN for all objects in the query. Either tool
can be run from the command line. To export a list of all objects in
Active Directory to a file called AllObjects.ldf, perform the following
steps:
1. | Log on to the Windows Server 2008 R2 system with an account with administrator privileges.
|
2. | Click Start, click All Programs, click Accessories, and select Command Prompt.
|
3. | Type cd \
and press Enter. The command prompt should reflect the local boot
drive. For this example, we assume that this drive is the C: drive.
|
4. | Type ldifde.exe –f AllObjects.ldf and press Enter.
|
5. | The root of the C: drive now contains a file named AllObjects.ldf. Open this file using Notepad and review the export.
|
6. | Back in the Command Prompt window, type ldifde.exe –f AllUsers.ldf –r "(objectclass=user)" and press Enter.
|
7. | The root of the C: drive now contains a file named AllUsers.ldf. Open this file using Notepad and review the export to see that only the user objects have been exported to this file.
|
8. | Type logoff and press Enter to log off of the server.
|
Ldifde.exe and csvde.exe
have similar switches, but the export file format will be different.
Also, each of these tools has a number of options that can be used to
perform advanced queries and only export a select list of objects. For
more information on these utilities, please reference the Help feature
by typing ldifde /? or csvde /? and pressing Enter in a Command Prompt window.
Note
This process does not include
security information, nor does it change the backup date on the
database; therefore, it does not provide the same level of data
protection as a “real” backup.
Exporting Active Directory Object Data Using PowerShell
Windows
Server 2008 R2 includes many PowerShell cmdlets for managing Active
Directory. A few examples of these include the following cmdlets:
Get-AdObject—
This cmdlet is used to read AD object data and return it to the screen
for reading, exporting, or piping into another cmdlet as a variable
value. Some other useful cmdlets that are close in functionality include
Get-AdUser, Get-ADComputer, Get-AdGroup, and several more.
Set-AdObject—
This cmdlet enables administrators to update attribute values on
specified Active Directory objects. Some other useful cmdlets that are
close in functionality include Set-AdUser, Set-ADComputer,
Set-AdOrganizationalUnit, and several more.
Remove-ADObject—
This cmdlet can be used to delete an object or several objects from
Active Directory, provided of course that deletion protection is not
configured for the desired objects. Some other useful cmdlets that are
close in functionality include Remove-AdUser, Remove-ADGroupmember,
Remove-AdOrganizationalUnit, and several more.
New-AdObject—
This cmdlet can be used to create new Active Directory objects. Some
other useful cmdlets that are close in functionality include New-AdUser,
New-ADGroup, New-AdOrganizationalUnit, and several more.
Restore-AdObject—
This cmdlet can be used to restore an Active Directory object that has
been previously deleted granted that the Active Directory Recycle Bin
has been enabled before the object was deleted.
More AD cmdlets that can be
used for common tasks include Unlock-AdAccount, Search-AdAccount, and
several more. All in all, more than 50 Active Directory-related cmdlets
are included with Windows Server 2008 R2 PowerShell. To perform a few
basic Active Directory export tasks using PowerShell, perform the
following steps:
1. | Log on to the Windows Server 2008 R2 system with an account with administrator privileges.
|
2. | Click
Start, click All Programs, click Accessories, click the Windows
PowerShell folder, right-click on Windows PowerShell, and select Run As
Administrator.
|
3. | Type cd \ and press Enter.
|
4. | Type Import-Module ActiveDirectory and press Enter.
|
5. | Type Get-Command *AD* -CommandType cmdlet
and press Enter. This returns all the Active Directory-related cmdlets
and also returns a few more cmdlets not related to Active Directory.
|
6. | Type Get-ADObject –Filter * and press Enter. This returns all the Active Directory objects to the PowerShell window with a default list of attributes.
|
7. | Type Get-ADObject –Filter * | Export-csv All-ADObjects.csv and press Enter. This returns all the Active Directory objects, writes the output to a .csv file instead of the window, and includes a default list of attributes.
|
8. | Type Get-ADObject –Filter * -Properties *| Export-csv All-ADObjects.csv and press Enter. This returns all the Active Directory objects, writes the output to a .csv file, and includes all populated attributes for each object.
|
The previous command is similar to the ldifde –f allobjects.ldf
command run in the previous section. For more granular exports, the
following list provides a few more examples of Active Directory cmdlets
commands that can be run in a PowerShell window with the Active
Directory module installed:
get-adobject -LdapFilter "(&(objectcategory=person)(objectclass=user))" -properties * |export-csv all-users.csv
get-adobject -LdapFilter "(&(objectcategory=person)(objectclass=contact))" |export-csv all-contacts.csv
get-adobject -LdapFilter "(&(objectcategory=computer)(objectclass=computer))" |export-csv all-computers.csv
get-adobject -LdapFilter "(&(objectcategory=group)(objectclass=group))" |export-csv all-groups.csv
Accidental Deletion Protection
A feature first released with
the Windows Server 2008 Active Directory Users and Computers snap-in and
included in the Windows Server 2008 R2 edition is an option to protect
an object from accidental deletion. Setting this option defines a Deny
permission to object deletion, so the result is not new, just the
simplicity in configuring it is new. To protect an object from
accidental deletion, perform the following steps of configuring this
option on the Administrator user account:
1. | Log on to the Windows Server 2008 R2 domain controller system with an account with administrator privileges.
|
2. | Click Start, click All Programs, click Administrative Tools, and select Active Directory Users and Computers.
|
3. | Select the View menu, and select Advanced Features.
|
4. | In the tree pane, select the Users container.
|
5. | In the right pane, locate the Administrator account, and double-click the user account to open the property pages.
|
6. | Select
the Object tab, check the Protect Object from Accidental Deletion check
box, and click OK to apply the changes, as shown in Figure 3.
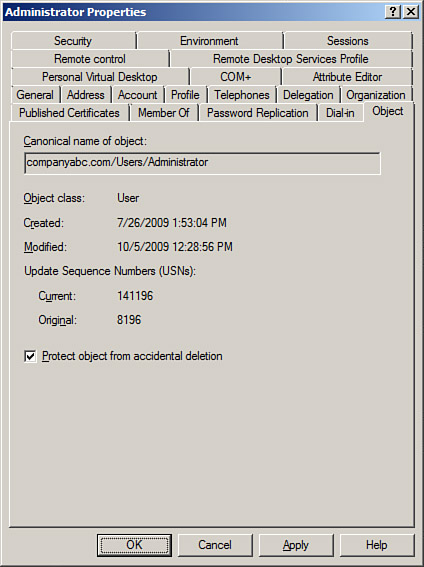
|
Using the Directory Services Restore Mode Password
When a Windows Server 2008 R2
system is promoted to a domain controller, the Directory Services
Restore mode (DSRM) password is created. This password is used only when
booting into Directory Services Restore mode. Restore mode is used when
the Active Directory database is in need of maintenance or needs to be
restored from backup. Many administrators have found themselves without
the ability to log on to Restore mode when necessary and have been
forced to rebuild systems from scratch to restore the System State data.
Many hours can be saved if this password is stored in a safe place,
where it can be accessed by the correct administrators. Now with Windows
Server 2008 R2, if a full authoritative restore of the entire Active
Directory database and sysvol folder is required, this can be performed
using the Windows Server Backup GUI. To perform the restore, the domain
controller will need to be booted into Directory Services Restore mode.
If a single object or a container with objects within is accidentally
deleted, it can be granularly restored by booting a domain controller in
DSRM, restoring the System State, and performing an authoritative
restore of the desired object(s). The issue with this is that the domain
controller is offline to client requests during the entire time it is
running in Directory Services Restore mode. To avoid this, Windows
Server 2008 R2 has a new feature called the AD Recycle Bin, which allows
for object recovery while the domain controller is online. This is
detailed in the next section.
There can still be cases where
restores will require booting domain controllers into DSRM and the DSRM
password will be required. To make sure this password is known, the
password can be updated regularly on all domain controllers. The Restore
mode password is server specific and created on each domain controller.
If the password is forgotten, and the domain controller is still
functional, it can be changed using the command-line tool ntdsutil.exe
from the command prompt. To update the DSRM password on a domain
controller named dc1.companyabc.com, perform the following steps:
1. | Log on to the Windows Server 2008 R2 system with an account with administrator privileges.
|
2. | Click Start, click All Programs, click Accessories, and select Command Prompt.
|
3. | Type cd \ and press Enter.
|
4. | Type NTDSutil.exe and press Enter.
|
5. | Type Set DSRM Password and press Enter.
|
6. | Type Reset Password on Server dc1.companyabc.com and press Enter.
|
7. | Type the new DSRM password, and press Enter.
|
8. | Type the new DSRM password again for confirmation, and press Enter.
|
9. | Repeat
the previous three steps for any additional domain controllers that
will have the DSRM password updated. To close out from NTDSutil.exe, type quit, press Enter, type quit again, and press Enter.
|
10. | Back at the command prompt, type logoff to log off of the domain controller.
|
Active Directory Recycle Bin
Windows Server 2008 R2
includes a feature that can be enabled called the Active Directory
Recycle Bin. When enabled, this feature can allow for a deleted Active
Directory object to be restored without having to restore the System
State of a domain controller and boot to Directory Services Restore mode
to perform a selective authoritative restore of that object. Enabling
the Active Directory Recycle Bin requires that all domain controllers
are running Windows Server 2008 R2, the forest functional level must be
set to Windows Server 2008 R2, and then functionality can be enabled
manually. To enable the Active Directory Recycle Bin, perform the
following steps:
1. | Log
on to a Windows Server 2008 R2 domain controller in the forest root
domain with an account with domain administrator privileges.
|
2. | Click
Start, click All Programs, click Accessories, click the Windows
PowerShell folder, right-click on Windows PowerShell, and select Run As
Administrator.
|
3. | Type cd \ and press Enter.
|
4. | Type Import-Module ActiveDirectory and press Enter.
|
5. | Type Get-ADForest and press Enter. Review the ForestMode value, which should be set to Windows2008R2Forest.
|
6. | If the ForestMode is not set to Windows2008R2Forest, for a forest named companyabc.com as an example, type Set-ADForestMode –Identity companyabc.com - ForestMode Windows2008R2Forest and press Enter. Type a Y and press Enter to confirm the change.
|
7. | Once the forest functional level is confirmed to be at the Windows Server 2008 R2 level, type in Get-ADOptionalFeature –Filter *
and press Enter. This returns the list of optional features, including
the Active Directory Recycle Bin. If this feature is enabled, the
EnabledScopes setting will have a value.
|
8. | Assuming that this functionality has not been enabled, as it is not enabled by default, type Enable-ADOptionalFeature 'Recycle Bin Feature' –Scope ForestorConfigurationSet –Target companyabc.com and press Enter.
|
9. | When prompted that this is an irreversible action, type Y and press Enter to enable the Active Directory Recycle Bin feature.
|
10. | After the command completes, type Get-ADOptionalFeature –Filter * and press Enter. Note that the EnabledScopes setting is now populated with a value, as shown in Figure 4.
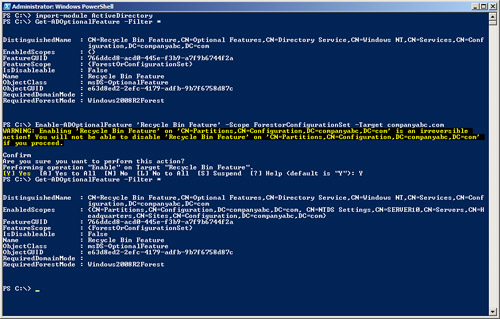
|
11. | Type exit and press Enter to close the PowerShell window.
|
After the Active Directory
Recycle Bin is enabled, it should be tested with test organizational
units, groups, users, or any desired objects. To perform a restore, the
Restore-ADObject cmdlets will be used along with a few other cmdlets to
get the preliminary information needed to restore.