The Configuration page in Server
Manager is somewhat misleading. This is not the page from which you
would configure the server. The Configuration node in Server Manager is
simply a container for the following four snap-ins:
These snap-ins enable
the administrator to control some elements of the server configuration
and are covered in the next four sections.
Task Scheduler
One of the greatly
expanded features of Windows Server 2008 R2 is the Task Scheduler. In
previous versions of Windows, this was an anemic service with limited
options and auditing features. The Task Scheduler features in Windows
Server 2008 R2 have been expanded into a more sophisticated tool. The
scheduler can start based on a variety of triggers, can take a number of
predefined actions, and can even be mitigated by conditions and the
settings.
Appropriately, there are
expanded elements to the Task Scheduler, as follows:
Triggers— Tasks run when the trigger criteria are
met. This could be a scheduled time, logon, startup, idle, log event,
user session connect or disconnect, or workstation lock or unlock. These
various triggers give the administrator a wide range of options on when
to start a task.
Actions— The
actions are the work that the task will perform. This can be executing a
program, sending an email via SMTP, or displaying a message on the
desktop.
Conditions— Conditions allow the task trigger criteria to be
filtered. Conditions include if the computer is idle, on battery power,
or connected to a network. This allows administrators to prevent tasks
from running if the computer is busy, on battery, or disconnected from
the network.
Settings— The settings control how a task can be executed,
stopped, or deleted. In the settings of a task, the administrator can
control if the task can be launched manually, if it runs after a missed
schedule start, if it needs to restart after a failure, if it needs to
run multiple tasks in parallel, or to delete it if it is not set to run
in the future.
Another big improvement is the
Task Scheduler Library, which includes approximately 40 different
predefined tasks. These tasks include the following:
ScheduledDefrag— This task runs every week and uses the command defrag.exe
–c to defragment all the volumes on
the server. This is a major improvement of previous versions of Windows,
which required this command to be run manually. The task runs at 1:00
a.m. every Wednesday of every week by default.
ServerManager— This task runs at user logon and runs the
ServerManagerLauncher to launch the Server Manager console whenever a
user logs on.
Both these tasks
demonstrate the capabilities of the Task Scheduler to automate routine
tasks or to ensure that certain tasks run at logon.
The Task Scheduler has a new
feature that goes hand in hand with the library, namely the ability to
create folders to store the tasks. This helps organize the tasks that
are created. The scheduler includes a Microsoft folder for the tasks
that ship with the operating system. Administrators can create other
folders to organize and store their tasks.
Selecting the Task Scheduler
folder in the Server Manager configuration shows the Task Scheduler
Summary (shown in Figure 1).
This window has two sections: Task Status and Active Tasks. The Task
Status section shows the status of tasks within a time frame (by
default, the last 24 hours). The time frame can be set to the last hour,
last 24 hours, last 7 days, or last 30 days. For each task that has run
within the time frame, it shows the Task Name, Run Result, Run Start,
and Run End. The section also summarizes the task status; Figure 1 shows that 13 total tasks have run with 1 running and
12 succeeded. The figure also shows that it is the System Performance 1
Hour data collector task that was created earlier that is running.
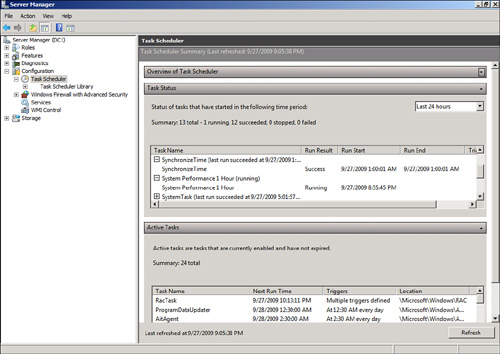
The Active Tasks name is
somewhat misleading because it shows tasks that are enabled and their
triggers. It does not show tasks that are running. For the scheduled
tasks, it shows the Next Run Time. This section is very useful for
seeing which tasks will run on a given server in response to a trigger,
either a schedule or an event. If the task does not appear in this
section, it will only be run if executed manually.
Windows Firewall with
Advanced Security
The Windows Firewall with Advanced Security
feature provides access to the combined Windows Firewall and Connection
Security features of Windows Server 2008 R2. These technologies work in
tandem to provide protection from network-based attacks to the server.
The firewall rules determine what network traffic is allowed or blocked
to the server. The connection security rules determine how the allowed
traffic is secured.
The Windows Firewall with
Advanced Security folder shows a summary of which profile is active
(Domain, Private, or Public), the profile’s high-level configuration,
and links to the other components of the snap-in.
The other components of the
Windows Firewall with Advanced Security snap-in are for configuration
and monitoring the features. These components are as follows:
The inbound and outbound rules control what
traffic is allowed in to and out of the server. There are several
hundred rules governing what traffic is allowed. These are organized
into profiles for ease of application. Table 1 shows these
profiles.
Table 1. Firewall Profiles
| Profile | Description |
|---|
| Domain Profile | Applied
when the server is connected to its Active Directory domain. |
| Private Profile | Applied
when the server is connected to a private network but not to the Active
Directory domain. |
| Public Profile | Applied when the server is connected to a
public network. |
Clearly, the vast majority
of services will have the Domain Profile active, as they will likely be
on a network with Active Directory. Each of the profiles has a set of
rules associated with it. In addition, a number of rules apply to all
profiles, which are designated as “Any.” Some of the rules are disabled
by default.
Connection Security rules are
stored in the likewise named folder. The rules specify how the
computers on either side of a permitted connection authenticate and
secure the network traffic. This is essentially the IPSec policy from
previous versions of Windows, albeit with a much improved interface. By
default, there are no Connection Security rules created in Windows
Server 2008 R2. Rules can be created and reviewed in this portion of the
snap-in.
The Monitoring folder is
somewhat limited in scope. It has a Firewall folder and a Connection
Security Rules folder. These two folders simply show what rules are
active, but show no traffic details or if the rules have blocked or
allowed anything. In effect, they show the net result of the profile
that is active.
Services
The Services snap-in in
the Configuration container in Server Manager is essentially unchanged
from the previous version of Windows. All the services are listed, along
with their status, startup type, and logon credentials.
From the Services
snap-in, administrators can control services on the server, including
the following:
Start or stop the
services.
Change the
startup type to set the service to start automatically, be started
manually, or even prevent the service from starting at all.
Change the account the
service runs under.
Set up recovery actions if the service stops, such as
restarting the service or even restarting the server.
View the configuration details of the service, such
as what the executable is, what the service name is (which is shown in
the Task Manager window), and what dependencies it has.
A feature that was added in
Windows Server 2008 and still available in Windows Server 2008 R2 is the
Automatic (Delayed Start) startup type. This is a setting used to
reduce the crunch of services starting all at once during bootup of the
server. All the services with the Automatic (Delayed Start) setting will
be started after the services with the automatic setting. This allows
all the services to come up automatically, but allows essential services
to start first.
WMI Control
The last
snap-in in the Configuration container of the Server Manager is the WMI
Control tool. This is a new tool that enables administrators to maintain
the Windows Management Instrumentation (WMI) configuration on the
server. Interestingly, the tool is not an integrated snap-in, but rather
a separate tool.
With the WMI Control tool, an
administrator can do the following:
- Back up and
restore the WMI repository.
- Change the default scripting
namespace (root\cimv2).
- Manage access to the
WMI via the Security tab.
Before the introduction of
the WMI Control tool, these tasks were difficult to accomplish.
For example, to back up the WMI
repository, perform these steps:
1. | Open the
Server Manager console.
|
2. | Expand the Configuration folder.
|
3. | Select the WMI Control folder.
|
4. | Select the Action menu and then Properties.
|
5. | Select the Backup/Restore tab.
|
6. | Select the Back Up Now option.
|
7. | Enter a filename with a full path. The file type will
be a WMI Recovery File (.rec).
|
8. | Click Save to save the file.
|
9. | Click OK to exit the tool.
|