3. Protecting Yourself from Unsafe and Unwanted Software
With the addition of
Windows Firewall, Internet Explorer's Protected Mode, and Windows
Defender, it has become much easier to keep unwanted software off of
your computer and to remove it when it does get installed. The use of an
antivirus program and sound surfing habits help increase safety and
security to a very high level. This section examines some best practices that help to keep your computer free from unwanted software.
3.1. To Trust or Not to Trust?
Microsoft offers a digital signing technology, called Authenticode,
that can be used to guarantee that an executable item comes from the
publisher it says it comes from and that it has not been changed,
deliberately or otherwise, since it left the publisher's hands. The
digital signature verifies each bit of the signed file by comparing it
to a hash value; if even a single bit of the file has changed, the
comparison fails and the signature is invalid. Windows 7 blocks
installation of any code that has an invalid signature—by definition,
this indicates that the program file is corrupt (possibly because it was
damaged during downloading) or that it has been tampered with.
A digital signature
doesn't promise that the signed item is healthy and benevolent. It
confirms only that the bits you're about to download are the authentic
work of a particular party and haven't been tampered with on their way
to you. However, it is prudent to regard an unsigned item, or an item
without a valid signature, as a potential threat.
Assuming the signature is
valid, you can use the information contained within that signature to
make an additional determination—do you trust the person or organization
that attached the signature to the file? If the publisher is reputable
and the Security Warning message reports that the item has been
digitally signed, you must then decide how much confidence you have in
the publisher.
Normally, you make
choices about whether or not to install a signed item on an individual
basis. But you can choose to trust a particular publisher and allow its
software to be installed automatically without any prompting. Or you can
decide that the publisher of a particular program is not trustworthy
and you do not want any products from that publisher to be installed on
your computer, under any circumstances.
3.2. Blocking Potentially Unsafe Downloads
How does deceptive
software end up on a computer? The simplest route is the most direct:
you click a link on a webpage or in an e-mail message that leads
directly to an executable file.
For example, an advertisement might make extravagant or alarming claims
about a free program, perhaps even embedding the link in a pop-up
window that looks like a warning dialog box generated by Windows. When
an unsophisticated computer user clicks the ad, the program offers to
install as an ActiveX control via an Authenticode dialog box, which can
easily be mistaken for an official Windows stamp of approval.
In some cases, the
setup routine for one program surreptitiously installs additional
programs in the background. When we installed one widely used
song-swapping program in a previous version of Windows, for instance, we
found that it installed four well-hidden
add-ons along with the main application, resulting in an increase in
pop-up advertisements and changes to the way the browser handled search
requests and mistyped URLs. The most vicious types of deceptive software
typically attempt to exploit security holes to install themselves
automatically, without your approval or even your knowledge.
It should come as no
surprise that the makers of this sort of software employ all sorts of
tricks to mislead, deceive, and cajole you into installing their wares,
by extolling the program's benefits and glossing over or omitting any
mention of its undesirable behavior. For someone with a basic
understanding of computer security issues, the principal security
concern when browsing is to ensure (insofar as it is possible) that
anything you download is safe and that any potentially undesirable
behavior is fully disclosed. If you share a computer or network with
unsophisticated computer users who cannot reasonably be expected to
consistently reject unsafe software, your goal should be to prevent them
from having to make potentially confusing choices in the first place.
When you click a link
that points directly to an executable program file, Windows displays a
Security Warning dialog box like this:
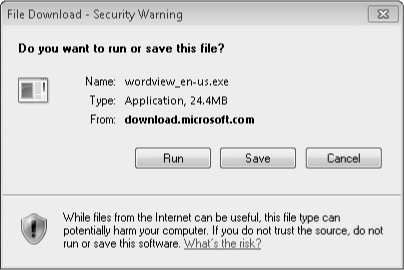
If you click Run, Windows downloads the file
to a temporary location and, when the download is complete, immediately
runs the executable program as if you had double-clicked it yourself.
If you click Save, you can download the file to a folder on your hard
disk. After the file is downloaded, you can click the Run button in the
Download Complete dialog box or click Open Folder to open Windows
Explorer, display the contents of the folder in which you saved the file, and double-click the file.
What happens next depends on the file type and whether the file is digitally signed:
If the
downloaded file is not executable, you see a warning dialog box asking
whether you want to allow the program associated with that file type to
open the downloaded file. In the example shown here, Windows is
attempting to open a Microsoft Office Word document using the Microsoft
Word Viewer program:
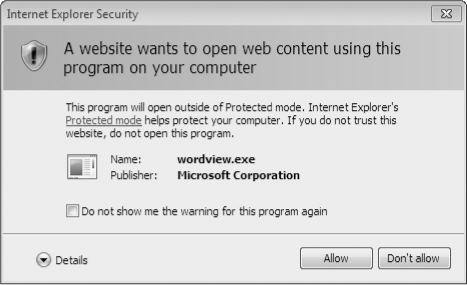
You can
allow or refuse the request. If you click Allow and select the Do Not
Show Me The Warning For This Program Again option, your choice is saved
and applied to all further examples of this type of content. If you
click Don't Allow, Windows ignores the Do Not Show Me The Warning For
This Program Again option even if you select it.
If the download is an unsigned executable file, you see a second Security Warning dialog box when you attempt to run it.
If the download is a signed executable file, you see a UAC dialog box that requires you to enter an administrator's credentials to continue.
If you're certain that the program is safe, you can continue with the installation.
|
When an executable file isn't digitally signed, it's impossible to make a definitive determination of
whether it's safe. In those circumstances, you can't be too cautious.
You can tip the odds in your favor by using common sense. Make sure the
download is from a verifiable source. Use your favorite search engine to
look for complaints about the program or its publisher; be sure to
search the web and popular newsgroups (see, for example, Microsoft
Technical Communities—w7io.com/0602),
and don't install anything until you're comfortable that you can
resolve any reported problems if they crop up on your PC. Be sure to
scan any downloaded files for viruses
and spyware before installing. Finally, set a System Restore point
before installing any software so that you can undo the configuration
changes if you're unhappy with the installation.
|
3.3. Controlling ActiveX
ActiveX
controls are small programs that run inside the browser window to
enhance the functionality of a website. They're used for such things as
enabling you to play games with other internet users, displaying stock
tickers, and displaying animation. Microsoft's various update sites use ActiveX
controls to compare installed patches and updates on your system with
those available on Microsoft's servers. ActiveX controls contain binary
code and, like executables that you run from the Start menu or a command
line, they have full access to your computer's resources, although they
are subject to some security restrictions.
Note:
You cannot download
an ActiveX control, scan it for viruses, and install it separately.
ActiveX controls must be installed on the fly. Although the inability to
scan for viruses in advance might sound like a security risk, you're
protected from known viruses if you've configured your antivirus
software to perform real-time scanning for hostile code. If the ActiveX
control contains the signature of a known virus or worm or engages in
suspicious behavior, the antivirus software will intercept it and refuse
to allow the installation to proceed. As with any program you download
and install, of course, you need to exercise caution and ensure that the
download is safe before allowing it on your computer.
Some businesses
refuse to allow the use of any ActiveX control that is not approved by
an administrator. Others disallow all ActiveX controls. If you need to
tighten the security settings imposed on ActiveX controls in the Internet zone, choose Internet Options from the Tools menu in Internet Explorer. On the Security tab, click Internet, and then click Custom Level. Then adjust options under the heading ActiveX Controls And Plug-Ins.